Modern software development moves at unprecedented speed, but rapid innovation often introduces security gaps that traditional approaches struggle to catch. DevSecOps addresses this challenge by embedding security directly into every phase of the development lifecycle rather than treating it as a final checkpoint. Organizations that successfully implement DevSecOps practices frequently report measurable risk reduction, faster remediation times, and stronger overall resilience. When executed strategically, these practices can improve an organization’s security posture by as much as 40%.
TLDR: DevSecOps integrates security into every stage of development, reducing vulnerabilities and accelerating response times. By automating security testing, enforcing strong access controls, and continuously monitoring systems, organizations can significantly reduce risk exposure. Practices such as shift-left testing, container security, and continuous compliance provide measurable security gains. When implemented holistically, these strategies can strengthen overall security by up to 40%.
1. Shift-Left Security Testing
Shift-left security moves testing earlier in the software development lifecycle. Instead of waiting for final QA stages, security checks begin during coding and design. This proactive approach allows teams to catch vulnerabilities when they are easier and less expensive to fix.
Integrated tools such as static application security testing (SAST) and software composition analysis (SCA) identify insecure coding patterns and outdated dependencies in real time. Immediate feedback empowers developers to address risks before they mature into exploits.
- Early vulnerability detection
- Lower remediation costs
- Improved collaboration between security and development teams
By embedding automated security scans directly into code repositories, organizations reduce late-stage surprises and strengthen foundational defenses.
2. Continuous Integration and Continuous Delivery (CI/CD) Security Automation
CI/CD pipelines streamline development, but without embedded security controls, they can accelerate the spread of vulnerabilities. Secure CI/CD pipelines incorporate automated security testing at every build and deployment stage.
Dynamic application security testing (DAST), container scans, and compliance checks can run automatically before code moves forward. This ensures only secure builds reach production environments.
Automating these processes eliminates reliance on manual reviews and significantly reduces human error. Teams gain confidence that each release meets predetermined security standards before reaching end users.
3. Infrastructure as Code (IaC) Security
Infrastructure as Code allows teams to manage infrastructure using configuration files. While this improves scalability and consistency, misconfigurations can introduce vulnerabilities across entire environments.
DevSecOps practices require scanning IaC templates for security risks such as:
- Open ports
- Weak encryption settings
- Improper access controls
Automated IaC security tools detect configuration weaknesses before deployment. By securing infrastructure definitions early, organizations prevent widespread exposure caused by flawed cloud setups.
4. Container and Kubernetes Security
Containers and orchestration platforms such as Kubernetes are central to modern application architecture. However, container images often include outdated libraries or insecure components.
Strong DevSecOps programs implement:
- Image scanning before deployment
- Runtime protection monitoring
- Role-based access control policies
Scanning base images for vulnerabilities prevents compromised containers from reaching production. Runtime monitoring further detects suspicious behavior once containers are live.

These layered defenses close common attack vectors in cloud-native environments, substantially reducing the attack surface.
5. Automated Compliance Monitoring
Regulatory compliance requirements continue to evolve across industries. Manual audits are time-consuming and often reactive. DevSecOps introduces automated compliance checks that continuously verify adherence to regulatory standards.
Continuous compliance monitoring tools compare infrastructure configurations and application behavior against predefined security baselines. When deviations occur, alerts trigger immediate corrective action.
This approach strengthens security by:
- Maintaining consistent adherence to standards
- Reducing audit preparation time
- Minimizing compliance-related penalties
Embedding compliance into the development pipeline transforms governance from a periodic review into an ongoing discipline.
6. Secrets Management and Identity Protection
Hardcoded credentials and exposed API keys remain common sources of breaches. DevSecOps emphasizes secure secrets management practices that remove sensitive information from source code.
Organizations implement centralized vault solutions to manage:
- API tokens
- Encryption keys
- Database credentials
Combined with strong identity and access management (IAM) practices, teams can enforce least-privilege access across systems. Restricting permissions limits lateral movement opportunities for attackers.
By automating credential rotation and eliminating embedded secrets, organizations dramatically reduce credential-based attacks.
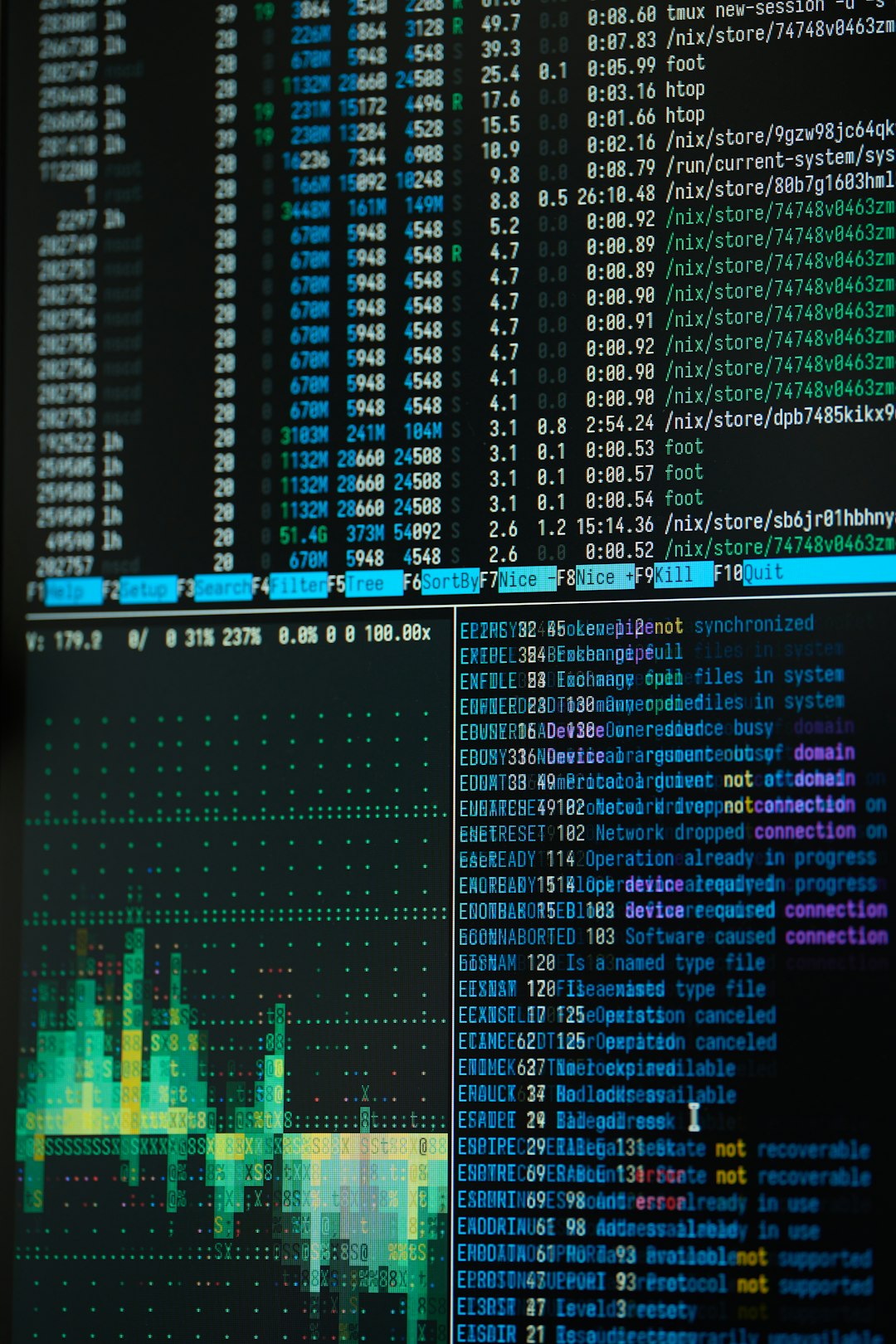
7. Continuous Monitoring and Threat Detection
Even the most secure development practices cannot guarantee zero vulnerabilities. Therefore, continuous monitoring becomes essential in identifying suspicious activities after deployment.
DevSecOps integrates logging, real-time telemetry, and behavioral analytics tools into production environments. These systems detect anomalies such as unusual login attempts, data exfiltration patterns, or unexpected spikes in traffic.

Machine learning-driven threat detection enhances response capabilities by identifying patterns that traditional rule-based systems might miss. Early detection shortens response times and limits potential damage.
8. Security as Code and Policy Enforcement
Security as Code formalizes security policies using machine-readable definitions. Rather than relying on documentation alone, organizations encode rules directly into automated workflows.
Examples include:
- Blocking deployments that lack encryption
- Preventing unapproved third-party libraries
- Enforcing network segmentation policies
This programmable approach ensures consistent policy enforcement across environments. Security standards become integrated into deployment gates, preventing risky configurations from progressing.
By shifting from advisory guidelines to enforceable code-based policies, organizations eliminate ambiguity and enhance accountability.
9. Security Culture and Cross-Functional Collaboration
Technology alone cannot strengthen security posture. DevSecOps requires a cultural shift that encourages shared responsibility between developers, operations teams, and security professionals.
Organizations that promote:
- Ongoing security training
- Open communication channels
- Collaborative threat modeling workshops
tend to cultivate stronger security awareness throughout the organization. When developers understand secure coding principles and security teams participate in early design discussions, vulnerabilities decline significantly.
A collaborative culture accelerates remediation timelines and ensures security considerations influence every release decision.
How These Practices Deliver a 40% Security Improvement
The cumulative effect of these nine practices creates measurable risk reduction. Shift-left testing eliminates vulnerabilities early. Automated CI/CD security prevents flawed builds from reaching production. Container scanning and IaC validation secure modern infrastructure environments.
Continuous monitoring and Security as Code enforce long-term consistency, while secrets management and access controls limit exploitable weaknesses. Finally, a strong security culture ensures every stakeholder contributes to resilience.
Together, these interconnected strategies reduce:
- Vulnerability remediation time
- Misconfiguration incidents
- Credential exposure risks
- Regulatory compliance failures
This layered defense model strengthens system integrity across development, deployment, and runtime phases. Organizations embracing DevSecOps as a comprehensive strategy consistently see better security metrics, fewer incidents, and improved customer trust.
Conclusion
DevSecOps transforms security from a reactive checkpoint into a proactive, continuous discipline. By embedding security into code, infrastructure, pipelines, and organizational culture, companies build resilience at every layer. The nine practices outlined above provide a structured, scalable pathway to enhancing security posture.
In a digital environment defined by constant change and growing cyber threats, integrating these DevSecOps methodologies is no longer optional. It is a strategic necessity that delivers measurable, sustainable security improvements.
Frequently Asked Questions (FAQ)
1. What is DevSecOps?
DevSecOps is a development methodology that integrates security practices into every stage of the software development lifecycle, combining development, security, and operations into a unified workflow.
2. How does DevSecOps differ from traditional security approaches?
Traditional security often occurs at the end of development. DevSecOps embeds automated security testing and monitoring throughout the entire lifecycle, making security continuous and proactive.
3. Can small organizations implement DevSecOps?
Yes. Many DevSecOps tools are scalable and cloud-based, making them accessible to startups and small teams seeking to improve security without extensive infrastructure investment.
4. Does DevSecOps slow down development?
When properly implemented, DevSecOps actually accelerates development by preventing costly rework and minimizing security-related delays later in the release cycle.
5. What tools are commonly used in DevSecOps?
Common tools include SAST, DAST, SCA scanners, container security platforms, CI/CD security plugins, infrastructure scanning tools, and monitoring solutions integrated within pipelines.
6. How long does it take to see security improvements?
Organizations often observe measurable improvements within months, particularly when they automate testing and implement continuous monitoring alongside cultural transformation initiatives.